You can find the most innovative laser marking machine
You can find the most innovative laser marking machine at LASIT. Stay up to date…Why should you focus for link building?

There are two things important for any website: great content and links. Link strategy …
Top 3 Reasons to Utilize Gym Management Computer Software

Buying or managing a fitness center is a task that is complicated. Staying in front …
Taking the First Steps to a Paperless Office

Making the change to a office that is paperless never ever been as easy as …
Top 4 PCB Surface Finishes – benefits and drawbacks
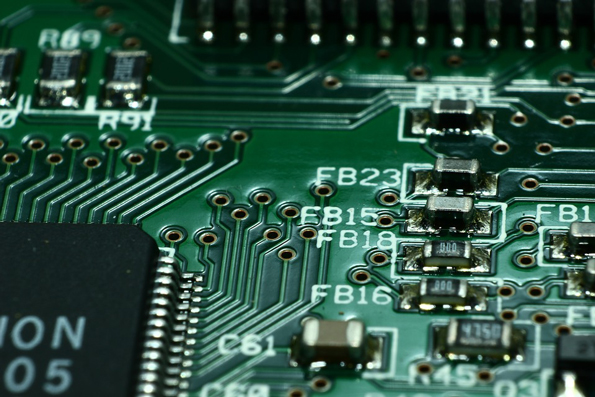
PCB Surface Finish Solutions Pros & Cons
PCB Surface finish form the interface that is …
Amazon Online Services History

There are loads of tales concerning the growth of AWS, nevertheless this much we all …
Serverless Computing: What You Need to Know

The term serverless grew in popularity as Amazon first launched AWS Lambda in 2014. Ever …
iPad Rental To Empower The Digital Training For Education

iPads are often served as the utmost versatile products at hand which are specifically designed …
Options For Hard Disk Drive Data Recovery

It’s important to appreciate the fact that all drives that are hard ultimately. You might …
Best Practices to Prevent Information and Privacy Breaches

Before we begin, let’s define what we’re talking about. The definition of protection breach can …